Cover letter sample . A PDF that shows what an ideal cover letter looks like
Cover Letter Tips:
- Write different cover letters for different kinds of jobs
- Tell a story to show more than what the resume can tell alone
- Describe what you can offer a prospective employer
- Describe how the customer can help the employer to succeed
- Use the customer’s own words
Resume Sample – A PDF to show you what an ideal resume should look like
Resume Template – A Word document that you can fill in to create a resume
Resume key words– A PDF that provides key words to use on resumes and in cover letters for different jobs
Resume worksheet . A Word document that can be printed and given to a customer before you start to create a resume
Resume Tips:
- Where possible, show up to 10 years of continuous employment. It is the customer’s preference whether to show more
- Include volunteer positions under Professional Experience when there are employment gaps
- Parsers (algorithms) use a hierarchy that is based on employer preferences. That’s why it’s imperative to use key words and list career highlights and qualifications/skills at the top of the resume
- Write a resume around the job description
- Write different resumes for different jobs/industries
- Show on-going education and learning (this makes the resume stronger)
- Eliminate all spelling and factual errors
Online Account and Application Record . An Excel spreadsheet to record online account information and to write progress notes
- NYS Dept of Labor account sign in, job information, job listings
- Unemployment Insurance (NYS Labor Dept) claim or certify benefits
- ID.me Identity verification used by several government agencies.
Step 1: Access your ID.me account if you have one when prompted or click on the “Create an ID.me account” link on the page to create one.
Step 2: Set up multi-factor authentication (MFA).
Step 3: Choose an approved document to submit (Usually State Identification).
Step 4: Upload your live photo.
Step 5: Enter your Social Security number.
The SUNY EOCs are a system of educational enterprises that serve eligible adult learners.
As part of this system, the Rochester Educational Opportunity Center will deliver comprehensive, community-based academic and workforce development programs and provide support services leading to enhanced employment opportunities, access to further education, personal growth and development.
REOC provides:
- High School Equivalency
- College Prep
- English for speakers of other languages
- Occupational Trades
- Early Childhood Development training and certification
- Business & IT training and certification
- Healthcare training and certification

OACES
30 Hart Street
Rochester, NY 14605
(585) IMPROVE (585-467-7683)
https://oaces.net
Earn your high school diploma. Prepare for post-secondary education. Train for a career.
Do what you need to succeed and live the life you want.
OACES provides:
- Adult education classes
- High School Equivalency (HSE) exam preparation and testing
- Career and technical training
- English classes for speakers of other languages
- Job placement assistance
- And more!

Center for Workforce Development Adult Education
The Center for Workforce Development (CWD) at Monroe 2-Orleans BOCES provides a variety of industry-aligned educational solutions to prepare you for the 21st century workforce.
- Career and Technical education programs
- High school equivalency diploma
- English classes for speakers of other languages
- Job placement assistance
- And more!
RHCSD
2034 Lehigh Station Rd
Henrietta, NY 14467
585-359-5000
The Rush-Henrietta Adult Literacy Program offers English as a Second Language classes for adults 21 and older at the beginning, intermediate, and advanced levels. Classes are taught by a New York state-certified teacher and offered during the day and evening. Students must be eligible for employment and/or seeking higher-level education to qualify. There is a $20 non-refundable registration fee. Classes are free of charge.
Classes take place at the Good Shepherd building, 3288 East Henrietta Road, Henrietta, NY 14467. Classes are held from 9:30 a.m. to 12:30 p.m. Monday through Friday, and from 6 to 9 p.m. Mondays and Wednesdays.
For more information and to schedule a registration appointment, call Pat Hantzis, program assistant, at 359-7918, or e-mail phantzis@rhnet.org.


1000 East Henrietta Road
Rochester, New York 14623
Phone: 585.292.2000
Monroecc.edu
Monroe Community College is a public community college in Monroe County, New York. It is part of the State University of New York. The college has two campuses; the main campus in the town of Brighton, and the Downtown Campus in the City of Rochester. The college also has off-site learning at the Applied Technologies Center, Monroe County Public Safety Training Facility and online
NYS Dept of Motor Vehicles – Permit or license, car registration, driving regulations
NYS Medicaid – New York’s Medicaid program provides comprehensive health coverage to millions of lower-income New Yorkers
NY State of Health Official Health Plan Market Place–Browse low-cost, quality health insurance options
NYS Social Programs – Learn about Social Programs offered for low-income individuals/households, people with disabilities, and veterans
NYS myBenefits – Create or login to your NYS benefits account to register for HEAP, SNAP, recertify your benefits, and more
NYS ACCESS (Adult Career & Continuing Education Services) – Resources to serve the education and employment needs of adults in New York State
Directory of all NYS Agencies – Locate the website, social media, and up-to-date contact for information for all NYS departments, agencies, and committees
Directory of all NYS Services – Find out how to apply for and access services such as the Empire Pass, applying for the Excelsior Scholarship, or starting an LLC
Government Benefits, Grants, and Loans – Learn about government programs that provide financial help for individuals and organizations
Medicare – Medicare is health insurance for people 65 or older. You’re first eligible to sign up for Medicare 3 months before you turn 65. You may be eligible to get Medicare earlier if you have a disability, End-Stage Renal Disease (ESRD), or ALS (also called Lou Gehrig’s disease).
NYS Dept. of Taxation & Finance – Tax information, file state returns
Internal Revenue Service – Tax information, account sign in, file federal returns
RGE – Gas and electric company.
Fairport Electric – Fairport gas and electric company.
Monroe County Water Authority – Authority created by New York State statute to supply clean water to residential, commercial and industrial customers
Spectrum – Television, phone, and internet service provider.
Greenlight Networks – Internet service provider
Frontier Communications – Internet, phone and TV service provider
T-Mobile – Home internet, phone service provider
All Choice Connect – Satellite communication service in Rochester, New York
Rochester Housing Authority – Apply for public housing.
Scammers Use Fake Emergencies to Steal Your Money
Examples of Family Emergency Scams
Scammers are good at pretending to be someone that they’re not. They try to trick you into thinking a loved one is in trouble. Here’s how the scam might work:
(View or share the YouTube version of this video.)
Here’s a real-life example of a family emergency scam:
(View or share the YouTube version of this video.)
If you get a family emergency scam call, here’s how it might go:
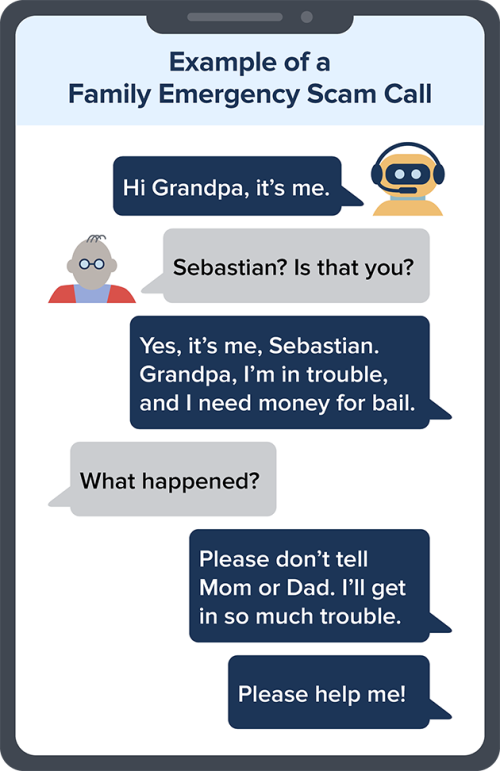
And once the scammer makes you think they’re your grandson and in trouble, they pressure you to quickly send them money. But it’s all a scam. Your family member was never in trouble. Slow down. Verify.
How Scammers Convince You
The scammer may already know a lot about you or the person they’re pretending to be. They may know your name, where you live, and other information they could have found on social media sites or by hacking a family member’s email. And sometimes they simply guess.
But they always say you have to pay right away by wiring money through a company like Western Union or MoneyGram, sending cryptocurrency, using a payment app, or by putting money on a gift card and then giving them the numbers on the back. Here are other tactics scammers use in fake emergency scams:
- Scammers might pretend to be an “authority figure,” like a fake lawyer, police officer, or doctor working with your family member. It makes them sound more convincing, and they hope it scares you.
- Some scammers use artificial intelligence (AI) to clone your loved one’s voice. With a short audio clip — maybe from content posted online — and a voice-cloning program, a scammer could call you and sound just like your family member.
What do fake emergency scams have in common?
- The scammer will say it’s urgent and that you’re the only one who can help.
- The scammer might tell you it’s important to keep it secret. They don’t want you talking to other family members and friends and realizing it’s a scam.
- The scammers will play with your emotions. They’re counting on you to act quickly to help your family or friend. And they’re counting on you to pay without stopping to check out whether there’s really an emergency. If you get a call like this, you can be sure this is a scam.
What To Do If You Get a Call About a Family Emergency
If someone calls or sends a message claiming to be a family member or a friend desperate for money, don’t trust the voice on the line — even if it sounds like your family member or friend. Scammers are good at faking it. Here’s what to do to verify the person’s identity:
- Resist the pressure to react and send money immediately. Hang up — or tell the person you’ll call them right back. If you don’t feel comfortable hanging up, try asking a question only the real person would know the answer to, like “What kind of dog do you have?” or “Where did you spend Thanksgiving last year?”
- Use a phone number you know is right to call or message the family member or friend who (supposedly) contacted you. Ask them if they’re really in trouble.
- Call someone else in your family or circle of friends, even if the caller said to keep it a secret — or sounds like a loved one. Do that especially if you can’t reach the friend or family member who’s supposed to be in trouble. A trusted person can help you figure out whether the story is true.
If You Sent Money to a Scammer
Scammers tell you to pay in a specific way. They often insist that you can only pay in ways that make it tough to get your money back — by wiring money through a company like Western Union or MoneyGram, sending cryptocurrency, using a payment app, or by putting money on a gift card and then giving them the numbers on the back. No matter how you paid a scammer, the sooner you act, the better. Learn more about how to get your money back.
Report Fraud
If you spot a scam, report it to the FTC at ReportFraud.ftc.gov and to your state attorney general.
*This information is from the FTC (Federal Trade Communications) Website
Tips on how to create a strong, complex password:
1) Use a combination of lower and uppercase characters, special characters (&^%) and numbers.
2) Uses passwords of at least 8 characters or more (the longer is better)
3) Create a long passphrase, a sentence or a phrase that includes a combination of upper- and lower-case letter, special characters, and punctuation (example: R@che$ter$Lilacfe$tiva!)
When making a password, avoid the following:
- Do not use your network username as your password.
- Don’t use easily guessed passwords, such as “password” or “user.”
- Do not choose passwords based upon details that may not be as confidential as you’d expect, such as your birth date, your Social Security or phone number, or names of family members or pets.
- Don’t use a consecutive string of numbers such as “1234”
Email is an old technology and it is inherently flawed. Consider following these guidelines to make yourself and your personal information more secure.
General Recommendations:
Passwords: there are two ways to create an email password: 1) use a combination of lower and uppercase characters, special characters (&^%) and numbers; or 2) create a long passphrase (It’s100%coldin Rochester)
Two email accounts: consider using one email account for family/friends, and another account for all business transactions. Why? Some companies will sell your data, and having a second account limits your exposure
Security Do’s: 1) if you suspect that your account with a business has been compromised, change your email password immediately; 2) change your password from time to time; 3) apply all software updates to your device
Security Don’ts: 1) don’t send sensitive information by email; 2) don’t store sensitive information in cloud services like Evernote and Dropbox; 3) don’t ever give out personal information in response to an email. Contact the sender using a number on the website from a trusted source, do not use the number, email, address, or any links given in the email.
Consider: using Gmail for your email account(s). It is less susceptible to spam and phishing than yahoo, Hotmail, Frontier, and AOL.
Definition: Spam is simply unsolicited email sent to a large number of recipients. For example, you book a hotel through hotels.com and suddenly you’re receiving email promotions from hotels.com
Remedy:
1) unsubscribe to company emails (at the bottom of the email you’ll find the unsubscribe function in small print)
2) when you create accounts online, look for settings that allow you to regulate the emails you receive
3) report the email as spam (you’re email provider will have an easy way to do this)
4) delete emails in your spam/junk folder. Remember first to review all emails in the folder, since some legitimate emails will end up there. When in doubt, report and delete.
Cyber Safety Tips
Internet-enabled crimes and cyber intrusions are becoming increasingly sophisticated and preventing them requires each user of a connected device to be aware and on guard.
- Keep systems and software up to date and install a strong, reputable anti-virus program.
- Be careful when connecting to a public Wi-Fi network and do not conduct any sensitive transactions, including purchases, when on a public network.
- Create a strong and unique passphrase for each online account and change those passphrases regularly.
- Set up multi-factor authentication on all accounts that allow it.
- Examine the email address in all correspondence and scrutinize website URLs before responding to a message or visiting a site
- Don’t click on anything in unsolicited emails or text messages.
- Be cautious about the information you share in online profiles and social media accounts. Sharing things like pet names, schools, and family members can give scammers the hints they need to guess your passwords or the answers to your account security questions.
- Don’t send payments to unknown people or organizations that are seeking monetary support and urge immediate action.
Cyber-Security-Quick-Reference
Current list of Cybersecurity Alerts & Advisories
*Information source FBI.gov
Phishing
Definition: The fraudulent practice of sending emails purporting to be from a reputable company in order to induce individuals to reveal personal information, such as password and credit card numbers.
Phishing emails will try to sell you something or gain access to your personal information. Sometimes, the phishing email appears to be from someone you know or from a company you’re doing business with.
Remedy:
1) always check the email address of the sender. If it is unfamiliar, then it is likely spam or phishing
2) never click on a link or attachment in a suspicious email
3) use your email provider to report phishing
4) text or call the individual or company listed as sender to verify the email is legitimate. Do not forward the email before verifying that it is legitimate
Ways to Check if a Website is Legit or Trying to Scam You
Hackers and Cybersecurity professionals put a lot of time and effort into making fraudulent websites look as legitimate as possible. Below are some ways to check if a website is legitimate or trying to scam you.
Carefully Look at the Address bar and URL
- Be sure that the site is secured by looking at the address bar (URL) to see if there is an “s” in the URL, which should look like this “https://” to start with or has a lock symbol in the address bar. This does not guarantee against a scam site, but it shows that the site owner is using secured encryption processes to transfer data and protect itself from hackers.
Check the Contact Page
- Review the options for contacting the company. If you don’t see multiple options (phone, email, live chat, or physical address) then proceed with caution.
- Note that one can fake contact details and may lead to calls being made to different call center’s which could lead to phishing scams
Review the Company’s Social Media Presence
- Most legitimate companies have some social media presence and activity. If you see the social media icons on their website, see if they link to a social media channel, and review the company reviews and see if you can find real employees of the company on LinkedIn.
- Though this would out multiple scams, it is still not a guarantee, if something looks “too good to be true, it isn’t”
Double Check The Domain Name
- Scammers will tend to create “similar” domain names to trick the user into thinking they are on a legit site, like Yah00.com or Amaz0b.net, making subtle changes that you may not even notice. Always double check the address bar to see if you have been redirected to a website that is not legitimate.
Look Up the Domain Age
- It is easy to look up the age of a website domain. Verifying the age of a site helps provide you with confidence that it has been in business for an established amount of time. Scam and fake sites usually have a short lifespan as they are rooted out early and shut down by legitimate business site owners.
Watch for Poor Grammar and Spelling
- Legitimate company websites will take great care in having a professional looking site. An excess of spelling, punctuation, and grammar errors could mean the website went up quickly. Occasional typos on a website can happen, but excessive errors could mean you are not on a legitimate site.
Walk Away If It’s Too Good to be True
- Though it is a common practice for some retailers to provide large price discounts on items to move inventory or promote a new product or service, if you find a site that offers an unbelievable deal, then think twice before continuing. If it’s too good to be true, then it probably isn’t legit.
Do Your Research
- A simple online search for the company’s reviews will tell you a lot about the business. See how recent the reviews are and if you see proactive responses from the company (where available.)
- Use the Better Business Bureau to research the reputation of a company.

ABC
400 West Ave
Rochester, NY 14611
585-325-5116
Action for a Better Community is a Community Action Agency that promotes and provides opportunities for low-income individuals and families to become self-sufficient.
ABC Programs:
- Action Front Center
- Bridges 2 Success
- Community Building in Action
- Employment Retention Investment Curriculum
- Energy Conservation Program
- Head Start & Early Head Start
- Health Career Programs
- High Impact Prevention Services for Youth
- High School Equivalency Prep
- Housing Grant Repair & Rehab Intake
- Office of New Americans
- Strategies to Success
- Strengthening Working Families Initiative
- Summer Youth Employment
- Training in Employment and Soft Skills
ABC
The Supplemental Nutrition Assistance Program (SNAP) is the largest federal nutrition assistance program. SNAP provides benefits to eligible low-income individuals and families via an Electronic Benefits Transfer card. This card can be used like a debit card to purchase eligible food in authorized retail food stores.
Eligibility is based of your Gross monthly income — that is, household income before any of the program’s deductions are applied — generally must be at or below 130 percent of the poverty line.
Applicants must live in the state in which they apply and meet certain bank balance limits. A household with an elderly (over 60) or disabled household member may have a higher bank balance limit.
You can apply online at Mybenefits.ny.gov, Download an application and mail to/drop off at 691 St. Paul St. Rochester, NY 14605, Call 585-753-6960 to have an application mailed to you, or you can pick up an application at 691 St. Paul St. Rochester, NY 14605.
If everyone applying is over 60 years old and/or disabled, you can use this new simplified application and mail to/drop off at 691 St Paul St. Rochester, NY 14605.
When the application is submitted, you will be screened for expedited benefits and, if eligible, the benefit will be issued within five business days. You will be contacted by phone for the screening interview, if applicable, and mailed an appointment for a SNAP telephone interview. You will not need to be seen in person.

Home Energy Assistance Program (HEAP)
HEAP 2024-2025 Regular HEAP benefit is scheduled to open on November 1st, 2024.
A federally funded program that assists low-income households in meeting the high costs of home heating. (heating supply can be natural gas, electric, oil, coal, propane, wood pellets, corn, or kerosene)
If you are eligible, you may receive one regular HEAP benefit per program year and could also be eligible for emergency HEAP benefits if you are in danger of running out of fuel or having your utility service shut off.
Eligibility and benefits are based on income, household size, the primary heating source, and the presence of a household member who is under age 6, age 60 or older or permanently disabled.
Benefits are given directly to the energy supplier not the recipient.
Your household may be eligible for a Regular benefit if:
A member of your household is a United States Citizen or qualified alien
Your household’s gross monthly income is at or below the current income guides for your household size
You receive Supplemental Nutrition Assistance Program (SNAP) benefits
You receive Temporary Assistance
You receive Code A Supplemental Security Income (SSI Living Alone)
| Base Benefit Amount | Living Situation |
|---|---|
| $21 | Eligible households that live in government subsidized housing or a group home setting with heat included in their rent. |
| $45 or $50 | Eligible households who have heating costs included as part of their rent. |
| $900 + applicable add-ons | Eligible households whose primary heat is oil, kerosene, or propane and who make direct payments to the vendor for heating costs. |
| $635 + applicable add-ons | Eligible households whose primary heat is wood, wood pellets, coal, corn or other deliverable fuel and who make direct payments to the vendor for heating costs. |
| $400 + applicable add-ons | Eligible households whose primary heat is electricity or natural gas and who make direct payments based on their household’s actual usage to the vendor. |
Regular Benefit Add-Ons for Households Paying Directly for Heat
The amount of the base Regular benefit will be increased by $61 if the household’s gross income is in the Tier 1 income range.
How to apply for Regular Benefits
Online:
at myBenefits.ny.gov
By phone:
(585)753-6209 or (585)753-6477
In-person:
You may apply in person at your HEAP Local District Contact.
In writing:
Print and mail the completed HEAP application
The 2024-2025 Emergency HEAP benefit is scheduled to open on January 2nd, 2025.
- Eligibility is based on income, available resources, and the type of emergency
Emergency HEAP benefits and eligibility are based on:
- income,
- available resources, and
- the type of emergency
You may be eligible for an Emergency HEAP benefit if:
- Your electricity is necessary for your heating system or thermostat to work and is either shut-off or scheduled to be shut off or
- Your electric or natural gas heat is off or scheduled to be shut-off or
- You are out of fuel, or you have less than one quarter tank of fuel oil, kerosene or propane or have less than a ten (10) day supply of wood, wood pellets, corn, or other deliverable heat source.
and
- Your household’s gross monthly income is at or below the current income guides for your household size as posted in the table below or
- You receive Supplemental Nutrition Assistance Program (SNAP) benefits or
- You receive Temporary Assistance (TA) or
- You receive Code A Supplemental Security Income (SSI) Living Alone and
- The heating and/or electric bill is in your name and
- Your household’s available resources are:
- less than $2,500; or
- less than $3,750 if any member of your household is age 60 or older, or under age 6.
| Type of Emergency | Amount |
|---|---|
| Heat Related Domestic (electric service required to operate heating equipment) | $185 |
| Natural Gas Heat Only | $400 |
| Natural Gas Combined with Heat Related Domestic | $585 |
| Electric Heat Combined with Heat Related Domestic | $585 |
| Non-utility heating fuel (oil, kerosene, and propane) | $900 |
| Non-utility heating fuel (wood, pellets, coal, corn, etc.) | $635 |
Heating Equipment Repair and Replacement
The 2024-2025 Heating Equipment Repair and Replacement benefit is scheduled to open October 1nd, 2024.
- If you are a homeowner and eligible, the Heating Equipment Repair and Replacement benefit can help you repair or replace your furnace, boiler and other direct heating equipment necessary to keep your home’s primary heating source working.
- Benefit amounts are based on the actual cost incurred to repair or replace your furnace, boiler, and/or other essential heating equipment, $4,000 for a repair and $8,000 for a replacement.
- You may call your HEAP Local District Contact to apply. An eligibility interview is required for all HERR applications, but may be completed with applicants in person or by telephone. Your local district contact will decide if you meet all the eligibility conditions, including the income and resource requirements. The district will provide more information on how to submit the application and required documentation.
Clean and Tune Benefit
The 2024-2025 HEAP Clean and Tune benefit is scheduled to open on October 1nd, 2024.
- Eligible households can receive energy efficiency services, which includes the cleaning of primary heating equipment, but may also include chimney cleaning, minor repairs, installation of carbon monoxide detectors or programmable thermostats, if needed, to allow for the safe, proper and efficient operation of the heating equipment. Benefit amounts are based on the actual cost incurred to provide clean and tune services, up to a maximum of $500. No additional HEAP cash benefits are available.
- Your household eligibility requirements include filing out a Clean and Tune benefit application with your local department of social services, providing all necessary documentation, and the household must reside in an eligible living situation.
Cooling Assistance Benefit
The 2024-2025 Cooling Assistance is scheduled to open April 15, 2025.
- If you are eligible, you may receive one Cooling Assistance benefit per applicant household for the purchase and installation of an air conditioner or a fan to help your home stay cool.
- In circumstances where an air conditioner cannot be safely installed, a fan will be provided.
- Only one air conditioner or fan, not to exceed $800 with installation for a window, portable air conditioner, or fan and not to exceed $1,000 for an existing wall sleeve unit, will be provided per applicant household. No additional HEAP cash benefits are available.

The Housing Choice Voucher (Formerly Section 8) Program is a federally-funded HUD program which subsidizes the rents of eligible low-income households.
Assistance is tenant-based. This means families can live in a qualifying rental unit of their choosing anywhere within the RHA jurisdiction or, if the family is eligible, they are able to “port” their voucher and move anywhere in the country.
For a unit to qualify for the program, the rent must be reasonable in comparison to other similar unassisted units in the area. The unit must also pass a Housing Quality Standards (HQS) inspection and maintain HQS standards throughout the term of the contract with RHA.
The family will typically pay 30 to 40% of their monthly income for shelter (rent plus utilities). RHA will enter a Housing Assistance Payments (HAP) Contract with the owner to pay the remaining balance.
Applicants on the Rochester Housing Authority Housing Choice Voucher Tenant-Based waitlist.
Eligibility for a housing voucher is determined by RHA and is based on the total annual gross income and family size. Eligible families cannot exceed the 50% of the median income for the Rochester area.
Eligible families must be US citizens and specified categories of non-citizens who have eligible immigration status. RHA will also examine the criminal background and prior Housing Choice Voucher history of any adult member of the household.
New Lobby Hours at 675 W. Main St.
[October 1, 2024] The lobby is now open Monday through Thursday 8:30 AM until 4:30 PM. It is best to arrive no later than 4:00 PM to be assured someone will be able to meet with you. The doors may close at 4:15 PM to new arrivals.It is also open on Friday from 8:30 AM until 12:00 noon. Try to arrive by 11:30 AM if you can.
Please be patient as we serve people in the order they arrive. We continue to do our best to serve and assist you!
– – – – – -= = = = = = = = = – – – – –
Update: Public Housing (not Housing Choice Voucher / Section 8) Waiting List
[September 6, 2024] Public Housing wait lists for 2, 3 and 4-bedrooms open on Monday, September 23, 2024 at 9:00 AM! Click >>HERE<< for more information.– – – – – -= = = = = = = = = – – – – –
Update: Housing Choice Voucher (Section 8) Waiting List
[July 17, 2024] The Housing Choice Voucher waiting list application process closed on June 14, 2024, at 4:00 PM. The Rochester Housing Authority is in the process of completing the random selection of 4000 applicants that will then be placed on the waiting list.
All applicants will be notified no later than 9/13/2024, to confirm whether they were place on the waiting list, or not. If placed, applicants will be invited to update their application by logging in to their existing account with the email address that they used to register.
Additional questions or concerns regarding this process may be directed to waitinglist@rochesterhousing.org, or by calling 585-697-6206.
The Low Income Household Water Assistance Program (LIHWAP) helps low income households pay the cost of drinking water and wastewater services.
The program can assist households who have past due bills (arrears) for drinking water and/or wastewater services.
LIHWAP can help prevent your drinking water and wastewater services from being shut off.
LIHWAP is a benefit based on the actual amount of water and/or sewer arrears, up to a maximum of $2,500 per water or sewer provider, or $5,000 if water and sewer services are combined, per applicant household. Benefits are paid directly to the household’s water and/or sewer vendor(s).
Eligibility is based on Income, Household, and amount owed.
Catholic Charities Family and Community Services provides housing, employment, and coordination of care to help people of all ages and all walks of life live independently with dignity while facing the challenges of addiction, aging, mental illness, HIV, poverty, intellectual and developmental disabilities, and immigration.
Services
Behavioral Health
Coordinated Care and Support for People of all ages
Employment and Independence
Housing and Stabilization
Intellectual & Developmental Disabilities
Refugee & Immigration Services
Support for Families & Children

RochesterWorks offers free employment and workforce development services for every job seeker – the parent, the caregiver, the student, the veteran, the upstart, the entrepreneur.
Services
5 Steps Program
Enhanced Programming
Group Programming
Individual Programming
Online training with Coursera
Recruiting Events
Selective Service Registration
Resources And Support Services
Ticket to Work
Training Grants
Job Readiness Training
Youth Career Center

Library Resource Outreach Center (LROC) is a collaboration between the Rochester Public Library and local human service agencies to offer services to the homeless, those in danger of becoming homeless, and those in need of access to the various resources listed below, without barriers.
• There are no eligibility standards for services
• No appointments necessary
• We work to eliminate or lessen barriers to other services
LROC is staffed by employees of Person Centered Housing Options, MC Collaborative, and Volunteer Legal Services as well as interns and volunteers.
LROC can connect patrons to services and resources, including:
• Housing
• Food
• Clothing
• Shelter
• Income
• Case management
• Medical care
• Legal assistance
• Employment
Central Library Hours & Contact
Tuesdays: 1pm-3pm
Wednesdays: 10am – 12pm
Thursdays: 1pm-3pm
Fridays: 1pm – 3pm
Phone: 585-428-8110
Email: libraryresourceoutreachcenter@gmail.com
LROC is located on the 3rd floor of the Bausch & Lomb Public Library Building of the Central Library of Rochester & Monroe County,
115 South Ave., Rochester, NY 14604
To start, here are the best questions to consider when purchasing a personal computer:
- What is your budget?
- What are you going to use the device for?
- Working from home, schoolwork, socialization, gaming, etc.
- Do you want a laptop (portable) or desktop (stationary)? If you want a laptop, do you want a 2-in-1, where the laptop can function as a tablet with touch screen features? Check out this 3-minute video that provides an overview of machines available today.
Computer retailers can recommend specific products for you based on the questions outlined above.
We recommend doing research on a product before you purchase it. Major computer retailers have review sections for their products on their websites. Another great resource for product reviews is Youtube. You can find a variety of reviews just by looking up “reviews for [insert device name here].” For example: “Reviews for Dell Inspiron 17 Laptop.”
Taking your research to the next level
If you really want to go the extra mile when researching products, you can investigate the device’s components to get an idea of the capacity of the machine you would be buying. PC hardware specifications, or specs, are a summary of a computer’s internal components and other system information.
Note: An in-depth knowledge of computer specs is not necessary when purchasing a computer. By answering the questions above and seeking the recommendation(s) of a professional, you can be confident in finding and purchasing a device that will meet your needs.
Computer Hardware Specifications For You to Consider
Operating System (OS): Refers to the powerful program that controls and coordinates a computer’s hardware devices and runs software and applications. Today, most devices have one of three: MacOS, WindowsOS, or ChromeOS.
Processor/Central Processing Unit (CPU): Provides the instructions and processing power the computer needs to do its work. The more powerful and updated your processor, the faster your computer can complete tasks.
Processor Speed: Measured in gigahertz (GHz) the higher the rating, the higher the performance of the computer’s processor.
Random Access Memory (RAM): Measured in size by gigabytes (GB), RAM stores short-term data that a PC requires to properly operate. The more RAM a device has, the better it will perform.
Storage capacity: Measured in gigabytes (GB), this refers to the capacity of the storage on a device, i.e. how many photos, videos, documents, etc. your device will store.
Move from Android to iPhone, iPad, or iPod touch -instructions from Apple on how to transfer data from an Android device to an iPhone
Move from iPhone to Android – instructions from Samsung on how to transfer data from an Android device to an iPhone
Move from Android to a Google Pixel Phone Instructions from Google on how to transfer data from an Android OS Device to a Google Pixel Phone.
Move from iPhone to a Google Pixel Phone Instructions from Google on how to transfer data from an iPhone to a Google Pixel Phone.
Android Support Page – Get manufacturer help for your Android device, searchable by brand
Samsung Support Page – a searchable page for operating all Samsung mobile devices, including set-up, basic operations, and advanced uses
Samsung User Manuals – provides links to the PDFs of all Samsung mobile device models, and provides instructions on how to access the user manual on your phone
iPhone User Guide – a searchable user guide on learning the basic of operating an iPhone
iPhone support page – a page of various weblinks for different iPhone uses including how to back up your data, managing your Apple ID, etc.
Apple’s iPhone Forum – a community forum for troubleshooting iPhone devices
iPad User Guide – a searchable user guide on learning the basic of operating an iPad
iPad Support Page – a page of various weblinks for different iPhone uses including how to back up your data, managing your Apple ID, etc.
Apple’s iPad Forum – a community forum for troubleshooting iPad devices
MacBook Pro Essentials An easy to navigate guide by Apple for all MacBook Pro devices. Use the site’s table of contents to learn how to set-up your device, what apps come with your device and what they’re for, FAQ’s, keyboard shortcuts, security features, and more!
MacBook Air Essentials An easy to navigate guide by Apple for all MacBook Pro devices. Use the site’s table of contents to learn how to set-up your device, what apps come with your device and what they’re for, FAQ’s, keyboard shortcuts, security features, and more!
Mac Tips for Users Switching from Windows Devices Learn how to perform some common tasks
on your Mac and popular keyboard shortcuts.
MacBook Manuals Type your device name into the search bar and view it’s user-guide. Did you know that you can access device manuals on every Apple device? Download Apple’s books app, type “Apple Inc.” into the search bar and you will see all of their manuals.
MacBook Forum A community forum for troubleshooting MacBook devices.
Move Android to MAC PC Instructions from Verizon on how to transfer data from an Android smartphone to a MAC PC.
New to Chromebook– Switch to a Chromebook, Set up your Chromebook, Migrate from Cloud Print, Set up your printer, Chromebook security
Chromebook shortcuts – Chromebook keyboard shortcuts
Chromebook support – Chromebook help
‘Windows’ refers to the operating system for PC’s developed by Microsoft. The term operating system (OS) refers to the powerful program that controls and coordinates a computer’s hardware devices and runs software and applications. Examples include Windows, Android, and iOS.
Make the Pointer AKA Cursor Easier to See on Your Windows PC
Find out Which Version of Windows Your Device is Running
Digital Learn is Interactive and adaptive software that allows you to learn digital skills.
Performing a Basic Search This 7-minute self-paced course is for anyone who has never used a search engine before. Learn about search engines and get started searching the internet
Intro to Email This 15-minute self-paced course is for any person new to email. Learn what email is, how to set-up an email account, how to reply to and send emails, and more.
NorthStar Digital Literacy offers curriculum, testing, and skills certifications for Digital Literacy volunteers and customers.
The NorthStar curriculum is aligned with the Minnesota Adult Basic Education Content Standards. Lesson plans are learner-centered and interactive. The lessons give learners multiple opportunities to build digital literacy skills through practice tasks and application of skills.
Lessons are independent of each other and are not required to be taught in sequence. They can be taught in order, or teachers may choose lessons for their class based on desired instruction for specific skills or standards.
Upon completion of each lesson, learners can take a NorthStar Digital Literacy Skills Assessment, on online, interactive test that emulates the actual software or website they are likely to use. Passing these proctored assessments provides students with a certification, which can be included on resumes and job applications to supplement their learned skills.
Take a sample assessment with NorthStar Digital Literacy online
Contact us to get set up with a NorthStar Digital Literacy Account
GCFGlobal.org program has helped millions around the world learn the essential skills they need to live and work in the 21st century by offering self-paced online courses.
From Microsoft Office and email, to reading, math, and more – GCF Global.org offers more than 200 topics, including more than 2,300 lessons, more than 2,000 videos, and more than 50 interactives and games, completely free.
TypingClub is the most effective way to learn how to type.
Learn touch typing online using TypingClub’s free typing courses.
It includes 650 typing games .
Keep practicing each lesson until you get all five stars.
Typing.com
Join millions of Typing.com users and learn to type at your own pace with free gamified lessons and student-led progression.
If you’re an Excel beginner, this is the perfect place to start. Excel Easy has several tutorials on how to use Excel.
Microsoft Excel is one of the most used software applications of all time. Hundreds of millions of people around the world use Microsoft Excel. You can use Excel to enter all sorts of data and perform financial, mathematical or statistical calculations.
Make the Pointer aka Cursor Easier to see on Your MacBook
Make the Pointer aka Cursor Easier to see on Your Windows PC or Laptop
Beginner’s and Senior’s Guide to Computers This extensive website goes through the basics of computer operation, using the internet internet, data, security, email, hardware, software. A passion project by a web developer with over 40 years of experience. Beginner’s and Senior’s Guide to Computers also has a blog and Youtube channel with video tutorials.
Techboomers.com Learn how to use sites, apps, and devices for free! They publish articles and videos that include introductions to popular websites and apps that describe what they are and how they can be useful. They also have lists of trips and tricks for certain websites, apps, and programs. Also check out their important primers on how people can protect their safety and privacy online against viruses, spyware, and scammers.
Senior Planet by AARP Senior Planet is a website that offers free classes, articles, videos, and activities to help seniors learn new skills. With a goal to connect older adults to tech and it’s many benefits, they offer free online classes, publish articles, and video tutorials.
LibreOffice is a free alternative to Microsoft Office. It includes six separate programs; the most popular are Writer, Impress, and Calc. Writer is work processor that is a free alternative to MS Word. Impress is used to make presentations, it is a free alternative to MS PowerPoint. Calc is a spreadsheet program that is a free alternative to MS Excel. LibreOffice is completely safe to use and download as long as you download it from their official website.
LibreOffice Help Page This page includes reference materials for every LibreOffice program. Use the Module List in the top left corner to open the drop-down list and select the LibreOffice program (ex: Writer) you’re looking for help with. Alternatively, you can navigate the page by clicking through the Contents Index in the left pane. You can also keyword search at the top of the page.
LibreOffice Program Guides Download free guides specific to each LibreOffice program or order a printed copy.
Office 365 Essential Reference Guide
Outlook 2021 Basic Reference Guide
Word 2021 Basic Reference Guide
Word 2021 Intermediate Reference Guide
Word 2021 Advanced Reference Guide
Excel 2021 Basic Reference Guide
Excel 2021 Intermediate Reference Guide
Excel 2021 Advanced Reference Guide
Lifeline provides up to a $9.25 monthly discount on service for eligible low-income subscribers and up to $34.25 per month for those on Tribal lands.
Subscribers may receive a Lifeline discount on either a wireline or a wireless service, but they may not receive a discount on both services at the same time.
Lifeline also supports broadband Internet service and broadband-voice bundles. FCC rules prohibit more than one Lifeline service per household.
Note: You may receive the lifeline benefit and the ACP benefit together if eligible.
Lifeline is available to eligible low-income consumers in every state, commonwealth, territory, and on Tribal lands.
The Lifeline program is administered by the Universal Service Administrative Company (USAC). USAC is responsible for helping consumers apply for the program, understand eligibility requirements, and keep their benefit current through an annual recertification process.
USAC’s website provides additional information regarding the program, including program requirements.
To participate in the Lifeline program, consumers must either have an income that is at or below 135% of the Federal Poverty Guidelines or participate in certain federal assistance programs, such as the Supplemental Nutrition Assistance Program (SNAP), Medicaid, Federal Public Housing Assistance, Supplemental Security Income, the Veterans and Survivors Pension Benefit, or certain Tribal Programs.
You can see if you are eligible by reviewing the information available at lifelinesupport.org (click “Do I Qualify?”).
Lifeline partners:

How Verizon Forward Works
Verizon Forward provides qualifying customers with Verizon Home Internet services
at a discounted price. If you participate in certain Federal Assistance programs such as SNAP,
you may qualify for the Verizon Forward discount.
Get Affordable Internet with Spectrum Internet Assist, available to qualified households
- In-home Wi-Fi service available
- FREE modem and Security Suite
- Limited-time offer
- No data caps and no contracts
Qualifications:
A member of your household must be a recipient of one of these assistance programs:
- National School Lunch Program (NSLP)
- Community Eligibility Provision (CEP) of the NSLP
- Supplemental Security Income (for applications age 65+ only

Community Broadband Network :
- Services the Finger Lakes Region. They will soon be contracting with the Monroe County to offer 100mb of service to 6,000 customers in certain Rochester City zip codes, for no more than $30 a month, locked in for 5 years.
- They are a community based, locally staffed. They believe in supporting the community they serve and that is why they never outsource our customer service or technicians. All of our staff is from Geneva, NY.
- There low cost pricing promise will last a life time for most plans. Your pricing will not change and you will never find hidden fees. There core value of transparency will always allow you to access your billing in real time.
- Premium customer service ensuring that you are connected 99.9% of the time. Rest assured that when you call our customer support line you will be connected to a live operator within 30 seconds of your call.
- Leading technology. Our world is changing everyday and don’t be left behind. DSL/Cable has not changed in over 20 years, but CBN is constantly evolving to provide you with next generation technology to provide you with high speeds.
- Giving back to the communities they serve. CBN is an active donor to local non-profit organizations and church groups. CBN’s mission is to create opportunities for those that are in need and helping communities flourish.

At Human-I-T, we create equitable access to opportunity by providing devices, internet access, digital skills training, and tech support for communities left on the wrong side of the digital divide—while at the same time, empowering businesses and organizations to do good by diverting technology from landfills to protect our planet.
We believe access to technology is a right, not a privilege. It’s what allows people to study remotely, apply for jobs, attend telehealth appointments, connect with distant family, or explore new ideas and perspectives.
This program provides:
– Laptops & Tablets
– Low-Cost Internet
– Digital Training
– Tech Support
Eligibility Requirements:
Proof can be submitted electronically, through text message, or in-person
at one of our locations at the time of purchase.
Government Assistance Program Accepted Proof:
- SNAP / EBT
- Medi-Cal / Medicaid
- SSI (Supplemental Security Income)
- SSDI (Social Security Disability)
- NSLP (National School Lunch Program)
- Public Housing Assistance or Section 8 voucher
- Lifeline
- Cal Grant Financial Aid
- Supplemental Nutrition Program for Women, Infants, and Children (WIC)
- California Alternate Rates for Energy (CARE)
- Head Start
- Temporary Assistance for Needy Families (TANF)
If the household does not receive any government benefits, they may provide proof of their yearly gross income. Households that make 250% of the federal poverty level threshold qualify for donations. Any documentation provided to prove income level must display dollar amounts that can be used to figure Annual Income. Must include the number of members in the household on purchase application.
Accepted forms of proof of income include:
- The prior year’s state, federal, or tribal tax return
- A Social Security statement of benefits
- Federal or tribal notice letter of participation in General Assistance
- A Veteran Administration statement of benefits
- A retirement/pension statement of benefits / Social Security benefits
Please note:
- Pay stubs are not accepted
- SNAP/EBT, Medi-Cal/Medicaid cards alone are not accepted.
A letter/document that confirms the active benefit is required. - The documentation must be dated within the last 6 months and it must be an active benefit.
- Households will be required to submit eligibility every 15 months.
If you meet the above eligibility requirements, please click either of the buttons below to access low-cost computers or low-income internet plans today.
If You’re Not Eligible
Don’t worry if you don’t meet our income eligibility requirements. You can still find plenty of low-cost computers, tablets, and smartphones from brands like Apple, Dell, HP, Intel, and Lenovo at our eBay store.
Plus, all proceeds from our eBay store go directly towards our efforts to shrink the digital divide and the e-waste stream.

PCs for People provides refurbished computers to eligible customers for affordable prices. We also provide low-cost high-speed internet solutions. Through computers, internet, digital skills training, and technical support, we work to ensure everyone has an equal opportunity to reach their full potential through digital technology.
Owning a computer and having internet service shouldn’t empty your wallet.
This program provides:
– Refurbished Desktop and Laptop Computers
– Low-Cost Mobile Internet
– Affordable Computer Repair
Please visit the website for more information about acceptable eligibility documentation. If you have questions about documentation that is not listed on the website, please contact one of the offices by phone or email. Any proof of eligibility is subject to approval by PCs for People staff. Additional documents may be required to unquestioningly prove income or enrollment in government assistance program. Once you have your documentation ready, there are three ways to send it in, online while placing an order, by email, or by faxing it to 651-666-1045.
Eligibility approval for online orders may take up to 2 business days. If you are eligible, you can purchase computers online, or come to one of our stores where computers are available ranging from $0 to $150.
Eligibility Requirements:
Qualifying Income-Based Assistance Programs
- Adult & Child Mental Health Case Management
- Employment Services (only if income-based in your state)
- Extended Foster Care
- Food Support (a dated letter showing current eligibility is required)
- Financial Assistance, such as GA, TANF, etc. (a dated letter showing current eligibility is required)
- Head Start
- Low-Income Home Energy Assistance Program (LIHEAP)
- Medicaid or Medical Assistance (bring a document that says “MA” or “Medical Assistance” on it)
- The National School Lunch Program’s Free or Reduced Lunch Program
- Section 8, Federal Public Housing Assistance, or Group Residential Housing (GRH)
- Section 42, Low Income Housing Tax Credit unit or other HUD low income program
- Social Security Disability (SSD)
- Supplemental Security Income (SSI)
- Federal Pell Grant
Qualifying Income Documentation
- The prior year’s state, federal, or tribal tax return (W2 forms or pay stubs are not acceptable)
- A Social Security statement of benefits
- A Veteran Administration statement of benefits (VA cards alone are not accepted)
- A retirement/pension statement of benefits
- An Unemployment/Workmen’s Compensation statement of benefits
- Federal or tribal notice letter of participation in General Assistance

The goal of the Computers with Causes is to provide a refurbished computer gifted by generous donors towards an educational, future learning program, foster home or disabled veteran in need.
This program provides:
– Refurbished computers
We get an overwhelming amount of gifted computer requests every year. We do a strict need assessment, background, and reference check, which helps us eliminate false requests and benefit those truly in need. If you or your organization truly “are in need”, chances are we will be in contact with you. Sometimes this can be weeks, so please be patient. We have a very limited volunteer staff and strive to meet all application demands in a timely manner.
Be advised that if you are currently receiving assistance from one or more of these sources (TANF, SSI, SSDI, Welfare, Food Stamps, etc..) acceptance of tangible property, gifts, financial assistance or services (Additional income) may affect or terminate your current benefits.
Please do not call our phone lines. Our phone lines are dedicated to accepting donations.
We invite anyone in need of a working computer to complete the application below. We have a full list of the causes we support (causes) with our main emphasis being the assistance of; students, teachers, and parents, the elderly, foster homes, shelters, disabled US veterans and struggling military families, and like-minded nonprofit organizations.
We do a strict need assessment, background and reference check, which helps us eliminate false requests and benefit those truly in need. If you or your nonprofit truly “are in need” and we are able to help, we will certainly contact you. Sometimes this can be weeks, so please be patient. We have a limited volunteer staff and strive to meet all application demands in a timely manner.
Please complete the form and tell us why you are a candidate for a gifted computer. Also be advised that if you are currently receiving assistance from one or more of these sources (TANF, SSI, SSDI, Welfare, Food Stamps, etc..) acceptance of tangible property, gifts, financial assistance or services (additional income) may affect or terminate your current benefits. After the application is submitted, we will review the information provided, then review our inventory, and if we are able to assist you then you will be contacted within 30 days. All applications are valid for 30 days, so if you do not hear from us within that time frame then you can apply again.
The Shore Foundation is now known as… Shift2
At Shift2 they are the connection point between companies that want to find a second home for their used computers, and the community members who can use that technology to support a strong future.
They highlight what technology can do when it shifts from being an internal corporate computer to being in the hands of its next owner.
They provide quality, used-business computers to organizations and charitable causes.